
Solutions: Sophos XG Firewall
The world’s best visibility, protection and response.
See it. Stop it. Secure it.



Expose Hidden Risks
Superior visibility into risky activity, suspicious traffic, and advanced threats helps you regain control of your network.
Stop Unknown Threats
Powerful next-gen protection technologies like deep learning and intrusion prevention keep your organization secure.Isolate Infected Systems
Automatic threat response instantly identifies and isolates compromised systems on your network and stops threats from spreading.
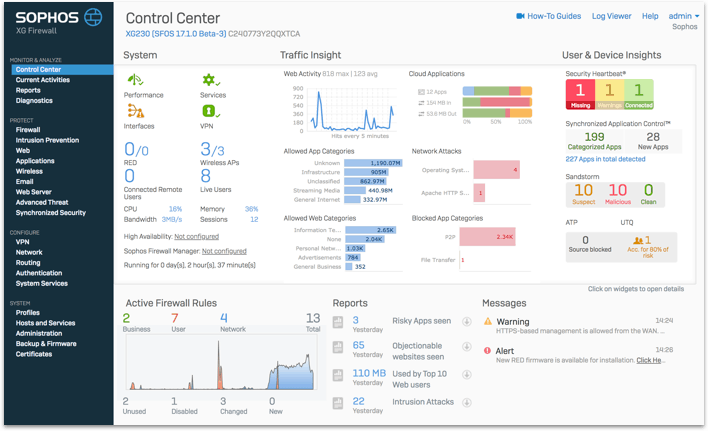
See Hidden Risks and Threats
LIKE YOU’VE NEVER SEEN BEFORE
Sophos XG Firewall provides unprecedented visibility into your network, users, and applications directly from the control center. You also get rich on-box reporting and the option to add Sophos iView for centralised reporting across multiple firewalls.
![]() TAKE IT FOR A TEST DRIVE.
TAKE IT FOR A TEST DRIVE.
Demo all XG Firewall’s features – no install, no commitment.
Online Demo
Stop unknown threats. Dead.
XG Firewall offers the best protection against the latest advanced threats like ransomware, cryptomining, bots, worms, hacks, breaches and APTs.
- Powerful Sandstorm sandboxing
- Deep learning with artificial intelligence
- Top performing IPS
- Advanced threat and botnet protection
- Web protection with dual AV, JavaScript emulation and SSL inspection
Powered by Deep Learning
An industry first, XG Firewall integrates Deep Learning technology into our Sophos Sandstorm sandboxing. It’s been developed by data scientists at SophosLabs to deliver the industry’s best detection rates without using signatures. It catches previously unseen malware lurking in suspicious payloads quickly and effectively. It’s just one of the ways that XG Firewall stops unknown threats dead in their tracks.
Intercepting Exploits
XG Firewall integrates some of the best technology from our leading Intercept X next-gen endpoint protection like exploit prevention and CryptoGuard Protection to identify malware exploits and ransomware before it gets on your network. Combined with our top performing Intrusion Prevention System (IPS) it doesn’t matter whether a hacker is trying to exploit a network vulnerability or an endpoint vulnerability, XG Firewall will stop it cold.Keep Your Network Under Control
A BREAKTHROUGH IN APPLICATION VISIBILITY AND CONTROL.
SYNCHRONIZED APP CONTROL
Automatically identifies hundreds of unknown, evasive, and custom Windows and Mac applications to easily prioritize the apps you want, and block the ones you don’t.
CASB AND CLOUD APP VISIBILITY
Cloud Application Visibility identifies all browser applications and cloud services to identify Shadow IT and data at risk to get it under control quickly and easily.
Watch Video

Isolate Infected Systems
Sophos XG Firewall is the only network security solution that is able to fully identify the source of an infection on your network and automatically limit access to other network resources in response. This is made possible with our unique Sophos Security Heartbeat™ that shares telemetry and health status between Sophos endpoints and your firewall.MONITOR NETWORK HEALTH
XG Firewall not only monitors host network activity but also receives health status directly from your endpoints so you have constant visibility into the health of your entire network.
IDENTIFY INFECTED SYSTEMS
XG Firewall instantly alerts you to compromised systems on your network with full details including the IP address, the user, and the process, so you’re not left digging for information.
AUTOMATICALLY ISOLATE INFECTIONS
XG Firewall uniquely integrates the health of connected hosts into your firewall rules, enabling you to automatically limit access to sensitive network resources from any compromised system until it’s cleaned up.A Firewall That Thinks Like You
SO YOU DON’T NEED TO THINK LIKE A FIREWALL.
We’ve rethought the way firewall rules and security policies are managed. Sophos XG implements an all-new powerful and flexible unified security and control model that enables you to see and manage all your user, application and network policies in a single place on a firewall rule basis.
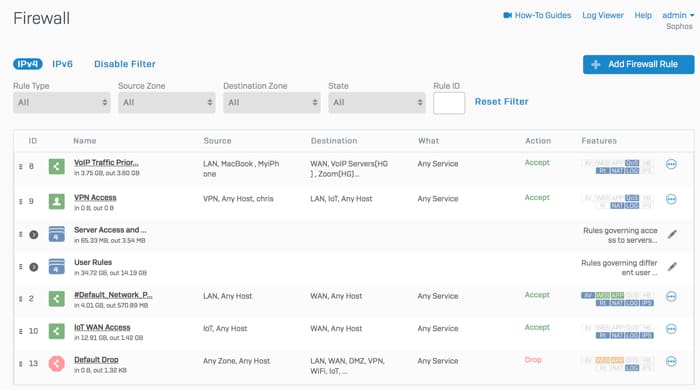
Most firewall products will have you setting up and managing security across multiple modules or screens. Not Sophos. We provide a powerful unified security model that allows you to easily establish and manage your security posture in one place.
Complete Next-Gen Protection
All the advanced networking, protection, user, and app controls you need to stay secure and compliant.Top Performing Protection
XG SERIES HARDWARE APPLIANCES PROVIDE INDUSTRY-LEADING PERFORMANCE AT EVERY PRICE POINT WITH THE ULTIMATE IN FLEXIBILITY, CONNECTIVITY AND RELIABILITY.
PURPOSE-BUILT TO PERFORM
Built with the latest Intel multi-core technology, generous RAM provisioning and solid-state storage on every model.FLEXIBLE CONNECTIVITY TO FIT YOUR NETWORK
We offer a variety of integrated and modular connectivity options to fit every business including WiFi, 3G/4G, DSL, and copper/fiber options up to 40GE.BUSINESS CONTINUITY
High availability deployment options and redundant power supplies and disks to ensure you never miss a bit or a byte.
Managed From the Cloud
Sophos Central is the ultimate cloud-management platform for all of your Sophos products – now including XG Firewall. It makes day-to-day setup, monitoring, and management of your network protection easy. With Sophos Central you can manage your entire Synchronized Security solution from a single console. Intercept X and the rest of the Sophos Suite of protection are all there at your finger tips: mobile, email, wireless and more.